What is CIA Triad?
CIA triad is the most common term used in the context of IT security. It gives us the most primary objective that we must work to protect as a cyber security community.
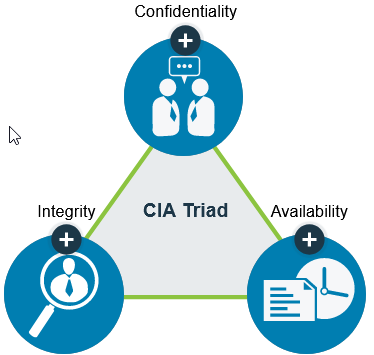
CIA refers to Confidentiality, Integrity and Availability.
Confidentiality: It means that the information is permitting only the authorized person to access the information while protecting them from being disclosed to unintended users.
Example: Me sharing my ATM pin to my spouse. I would not want anyone else to eavesdrop and hear the pin. If they do, then my confidentiality is breached.
Integrity: When information or data is used, maintained and recorded by ensuring it is complete, accurate, consistent and useful for the mentioned purpose. It means that the information is not altered by an unintended person.
Example: If I send a message my brother to handover a $100 to a third person. If the message gets altered and my brother is asked to handover a $500 to that person, then data is incorrect resulting in an unwanted situation.
Availability: Availability is achieved if the information that I desire is available at the time I want as a consumer of that data.
Confidentiality becomes difficult to achieve when we have so many users connecting from different devices with myriad number of applications. We never know which ones of those devices of apps are compromised/vulnerable. Therefore, it becomes very important to ensure that only authorized users and computers are allowed to access our network or critical servers.
Authentication
When a user says that they are someone or they have a valid password/authenticator, it is very important to validate that they are the rightful owners of that identity. In other words, they are who they claim to be. This process of proving one’s identity is called authentication.
Authentication Methods:
The three common methods of authentication are:
- Something that you know or knowledge-based: passwords, paraphrases ( these are most commonly used)
- Something that you own/have or token-based: smart cards, tokens, pins etc.
- Something you are or Characteristic-based: Biometrics, gait etc.
Use of only one method of authentication is called single-factor authentication (SFA), whereas two or more of these methods is known as multi-factor authentication (MFA).
Non-Repudiation
Non-repudiation protects us against a person falsely denying some action that they committed, such as information they shared, approval he/she granted etc.
Non-repudiation is particularly important in today’s time when the opportunities for identity theft and impersonation is rampant over digital mediums. It ensures that people are held responsible for transactions they conducted.
Privacy
Privacy is one of the important components of Information Security. Privacy refers to an individual’s right to protect or have control on the distribution of any information pertaining to the individual. With our data increasing being collected and stored digitally, privacy legislation and the requirement to ensure compliance is also growing. These regulations can span beyond borders, especially with the reach of the data at international level.
One example of such law with multinational implication is General Data Protection Regulation (GDPR). GDPR is a privacy law passed by European Union (EU), which is applicable to all organizations, nationally or internationally, conducting business in EU or having any persons in the EU. Organizations operating in the United States (US) may also be required to comply with this requirement if they handle any data pertaining to the citizens of the EU.
Similarly, in the US, there is Health Insurance Portability and Accountability Act (HIPAA) which controls how the privacy of the medical information is protected.It, therefore, is very important to be aware of various privacy laws and regulations in all jurisdictions where the company operates.