NETWORK : A network is a group of devices or computers connected together in order to share resources. Network Security, therefore, refers to all the technology, devices, processes and systems used to secure the CIA (Confidentiality, Integrity and Availability) of the connected computers and the information/data stored therein.
Securing a network requires the inclusion of both Software as well as Hardware solutions.
Hardware Security solutions: The hardware refers to the physical devices which are installed in the network to ensure security. Example of hardware solutions includes firewall, Intrusion Detection System (IDS), Intrusion Prevention System (IPS), surveillance cameras etc.
Software Security solutions: The software solutions for protecting the network are installed at the host level or in the devices. Examples of Software security solutions include antivirus, host firewall, etc.
- Antivirus software: Antivirus software are installed on the user devices such as laptops, desktops and mobiles to block malicious files/softwares from running.
- Host firewall: Host firewalls are different from the network firewall appliances in that they are software installed on our system and not tangible physical appliance. Windows Defender Firewall is an example of host firewall which comes pre-installed with the MS Windows Operating system.
In order to protect a network, it is vital to know the various Tactics, Techniques and Procedures (TTPs) of an attacker. By knowing the various pathways the attacker may take to compromise our network, we can get insights on how to protect it. The most common set of consecutive actions taken by an attacker is summed by by Lockheed Martin via the Cyber Kill Chain.
The Lockheed Martin Cyber Kill Chain consists of 7 steps as below:
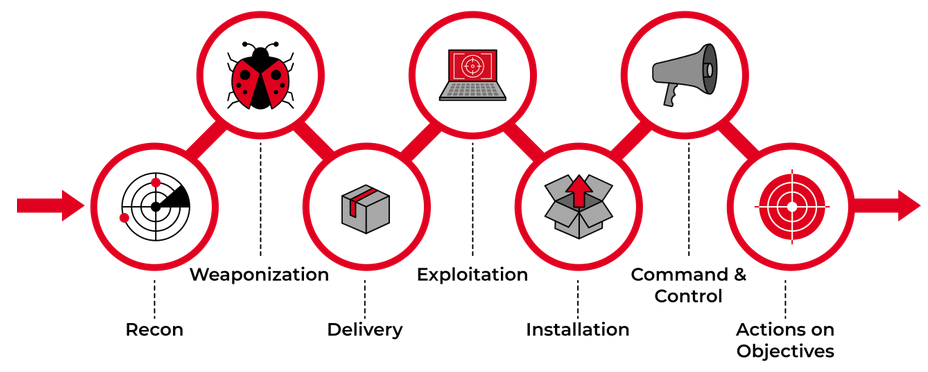
These steps outline the general steps involved in intruding into a network by an attacker. The steps include:
i. Reconnaissance: The attacker gathers as much information as possible about the target network. They gather various information such as the systems and software being used by the target, the behavioral and other related information about staffs too. In order to perform the reconnaissance, they do scanning of the network. The scanning may be consisted of two types:
- Active scanning: The attacker scans the network by interacting with the target’s system, such as port scanning.
- Passive scanning: The attacker conducts scanning by gathering information from information found in the public domain, such as Open Source Intelligence (OSINT).
ii. Weaponization: The attacker prepares a malicious file so that they can use it to gain access.
iii. Delivery: This stage involves delivery of the weaponized code to the target with any meduim, such as a usb drive.
iv. Exploitation: The target executes the malicious file on the victim’s system.
v. Installation: The executed file will install malware on the victim’s computer.
vi. Command & Control: The attacker now gains a way to control the victim’s system by setting a command and control.
vii. Actions on Objective: Now, the victim is fully compromised. The attacker has now achieved their objectives, whether it is destroying the devices connected to it, exfiltrating data or using the system as a bot.